The Legal Loophole That Lets the Government Buy Its Way Around the Fourth Amendment
Long before you see a targeted ad for that pair of shoes you briefly mentioned in a text, your digital profile has likely been auctioned, analyzed, and archived. In the time it takes to refresh your social media feed, hundreds of data points regarding your location, interests, and associations are traded in a marketplace that operates almost entirely in the shadows. For years, this invisible commerce has served the advertising industry. Today, however, it serves as the foundation for a much more intrusive architecture: the American surveillance state.
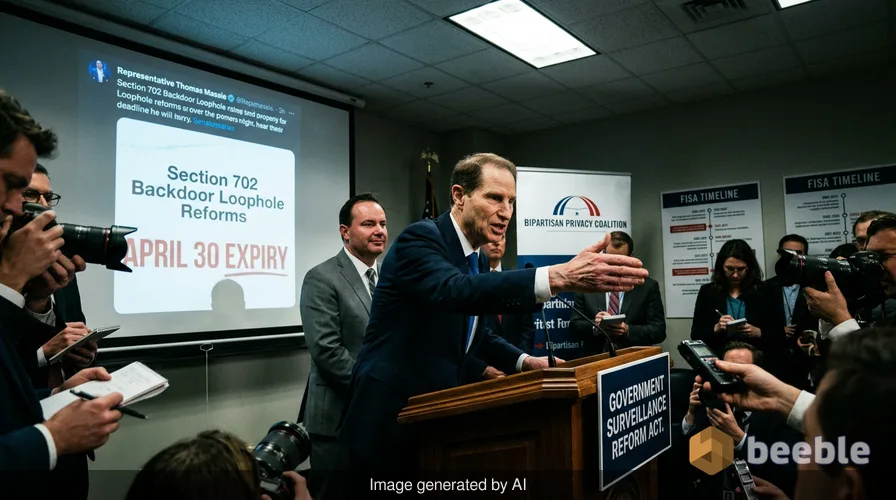
As we approach the April 30 deadline for the expiration of Section 702 of the Foreign Intelligence Surveillance Act (FISA), Washington is locked in a high-stakes standoff. At the heart of the debate is a fundamental question of digital hygiene: Can the government bypass the U.S. Constitution simply by opening its checkbook? While the law was originally designed to track foreign threats, it has evolved into a systemic dragnet that captures the private lives of millions of Americans. As a digital detective who has spent years peeling back the layers of corporate privacy policies and government overreach, I’ve seen how these legal frameworks are often built like a patchwork quilt—full of holes that the average citizen never notices until they fall through one.
The 'Foreign' Law with a Domestic Reach
Section 702 is often described by the intelligence community as a crown jewel of national security. In principle, it allows agencies like the National Security Agency (NSA) and the CIA to collect communications from non-U.S. citizens located outside the country. Because much of the world’s internet traffic flows through servers physically located on American soil, this law grants the government a de facto master key to global communications.
However, there is a catch that privacy hawks have long warned about: incidental collection. When a foreign target emails an American citizen, or when an American discusses a foreign contact in a message that happens to pass through a monitored server, that data is swept up. To put it another way, Section 702 is like a fishing net designed for tuna that inadvertently catches thousands of dolphins. Under current rules, once that 'dolphin' data—the communications of Americans—is in the government’s possession, the FBI can often search it without a warrant. This is the infamous 'backdoor search' loophole, a practice that allows domestic law enforcement to sidestep the Fourth Amendment’s requirement for probable cause.
Shadow Cartographers: Buying Your Way Past the Bill of Rights
While the backdoor search is a significant concern, a more modern and perhaps more precarious threat has emerged: the commercial data broker loophole. In the physical world, we would never allow a private investigator to follow us 24/7, noting every doctor’s visit, political rally, or late-night grocery run. Yet, we carry devices that do exactly this, and we 'consent' to it through terms of service that resemble a labyrinth more than a legal agreement.
App developers collect reams of granular location data and sell it to data brokers—the shadow cartographers of the digital age. These brokers then sell the data to the highest bidder, which frequently includes federal agencies. During a recent congressional hearing, FBI Director Kash Patel confirmed what many of us in the privacy community have long suspected: the Bureau buys Americans’ location data without seeking court authorization.
From a compliance standpoint, the government argues that since this data is 'commercially available,' it does not require a warrant to access. Essentially, they are treating your constitutional rights as a commodity that can be circumvented if the data is purchased on the open market rather than seized. This practice turns the digital footprints we leave behind into a trail of breadcrumbs that the government can follow without ever having to explain itself to a judge.
The Legislative Standoff: Reform vs. Status Quo
Lawmakers are currently split into two camps. On one side, a bipartisan coalition led by Senators Ron Wyden and Mike Lee has introduced the Government Surveillance Reform Act (GSRA). This bill is a sophisticated attempt to modernize our privacy laws for the 21st century. It seeks to close the backdoor search loophole by requiring warrants for searches of Americans’ data and, crucially, it would ban the government from purchasing personal data from brokers.
In contrast, the White House and some leadership in both parties are pushing for a 'clean' re-authorization. This would extend Section 702 in its current form, maintaining the status quo. Recent social media posts from President Trump suggest the administration is keen on preserving these powers without additional hurdles. The tension is palpable. For those of us who value transparency, the push for a simple extension feels like building a house on a crumbling foundation—eventually, the lack of oversight will lead to a systemic collapse of public trust.
AI and the New Frontier of Surveillance
Adding another layer of complexity to this debate is the rapid integration of artificial intelligence into the surveillance apparatus. The U.S. government is currently in nuanced negotiations with AI leaders like Anthropic and OpenAI. The goal? To use advanced AI models to analyze the billions of location points and communication logs collected under Section 702 and through commercial purchases.
This is where the 'toxic asset' of data becomes truly dangerous. When AI is applied to mass surveillance, the government isn't just looking for a needle in a haystack; they are building a machine that can map the entire haystack in real-time. This capability makes privacy-preserving legislation even more urgent. Without stringent rules, the combination of warrantless data access and AI-driven analysis creates a level of intrusive power that the authors of the Bill of Rights could never have imagined.
The Danger of Secret Law
Perhaps the most troubling aspect of this debate is the existence of what Senator Wyden calls 'secret law.' As the longest-serving member of the Senate Intelligence Committee, Wyden has warned that multiple administrations have relied on a secret legal interpretation of Section 702 that directly affects the privacy rights of Americans.
When the rules governing surveillance are opaque, they are impossible to challenge. In a democratic society, the law should be a compass—a clear guide that tells both the citizen and the state where the boundaries lie. When those boundaries are hidden in classified memos, the relationship between the government and the governed becomes fundamentally broken. Wyden’s call for declassification is not just about transparency; it is about the actionable right of citizens to know how they are being watched.
Taking Control of Your Digital Identity
While the battle in Congress continues, you don't have to wait for a legislative fix to start practicing better digital hygiene. Compliance with your own personal privacy standards is the first step toward reclaiming your digital identity. Here are a few empowering steps you can take today:
- Audit Your App Permissions: Go to your smartphone settings and look at which apps have 'Always On' access to your location. If a weather app or a calculator doesn't need to know where you are at 3:00 AM, revoke the permission.
- Opt-Out of Data Brokers: Use tools and services that help you submit deletion requests to major data brokers. While it won't erase your entire digital footprint, it makes you a much harder target for 'shadow cartographers.'
- Use End-to-End Encryption: Whenever possible, move your sensitive conversations to platforms that use end-to-end encryption. Think of it as a sealed envelope for your digital life—even if the 'mail carrier' is forced to hand over the data, they won't have the key to read what's inside.
- Support Transparent Legislation: Reach out to your representatives and let them know that any re-authorization of Section 702 must include the reforms found in the Government Surveillance Reform Act.
Ultimately, privacy is not about having something to hide; it is about having something to protect. As the April 30 deadline looms, the choice for lawmakers is clear: they can either reinforce the walls of the Fourth Amendment or allow them to be further eroded by the convenience of the digital age.
Sources:
- Foreign Intelligence Surveillance Act (FISA), Section 702.
- Government Surveillance Reform Act (GSRA) of 2024/2026.
- Fourth Amendment to the United States Constitution.
- Congressional Testimony of FBI Director (March 2026).
- Official Statements from the Office of Senator Ron Wyden.
Disclaimer: This article is for informational and journalistic purposes only and does not constitute formal legal advice. If you have specific concerns regarding your legal rights or data privacy, please consult with a qualified legal professional.



See you on the other side.
Our end-to-end encrypted email and cloud storage solution provides the most powerful means of secure data exchange, ensuring the safety and privacy of your data.
/ Create a free account

