The 'Ethical' Spyware Mirage: Why Paragon is Ghosting Italian Prosecutors
Long before a journalist receives a notification from Apple or WhatsApp warning them of a state-sponsored attack, a deal is struck in a quiet office. These deals—worth millions—trade in the currency of our digital lives. But while the sales pitches are polished and the marketing brochures promise 'security and ethics,' the reality of the spyware industry often looks more like a disappearing act.
For over a year, Italian prosecutors have been chasing a ghost named Paragon Solutions. This Israeli-American company, once heralded as the 'righteous' alternative to the scandal-ridden NSO Group, has reportedly gone silent. Despite previous public theatrics where the company claimed it wanted to help investigate hacking allegations, Paragon has failed to respond to formal judicial requests for information. As a journalist who spends my days communicating through encrypted tunnels and verifying code, this pattern of 'accountability until it actually matters' is a scenario I have seen play out far too often.
A Midnight Knock in Milan
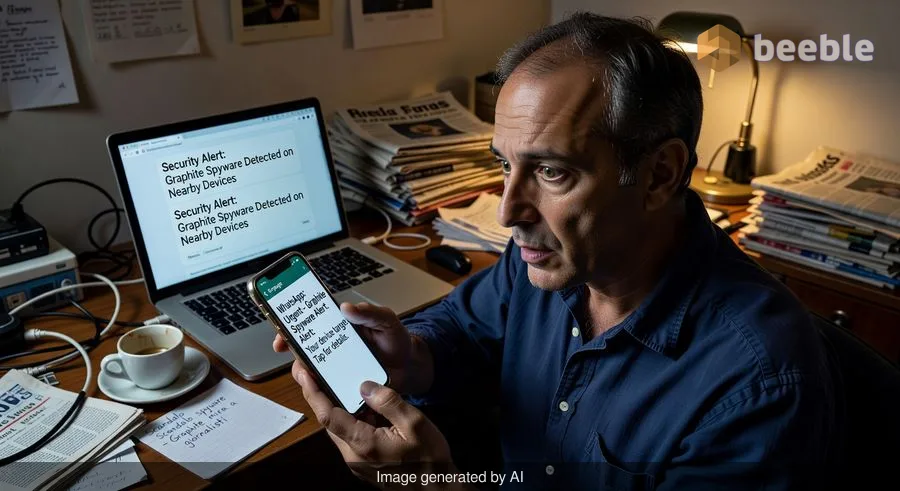
The scandal began not with a physical knock, but with a digital one. In late 2023, WhatsApp and Apple sent notifications to a group of Italian journalists and activists. The message was chilling: their devices had been targeted by government-grade spyware. Among the targets were Francesco Cancellato and Ciro Pellegrino, journalists at the news site Fanpage, and members of Mediterranea Saving Humans, a nonprofit dedicated to rescuing migrants.
WhatsApp’s forensic analysis pointed directly at 'Graphite,' a sophisticated surveillance tool developed by Paragon Solutions. In the world of digital espionage, Graphite is a digital skeleton key. It doesn't just watch what you do; it siphons data from the cloud, bypassing many of the traditional security measures users rely on to keep their private conversations private.
When the news broke, the Italian public was rightfully outraged. Prosecutors in Milan and Rome opened investigations. At first, Paragon took a bold, almost defiant stance. They publicly called out the Italian government, claiming they had offered to help investigate if a journalist was hacked but were rebuffed. In a move of high-stakes corporate theater, Paragon even announced it was canceling its contracts with Italy’s internal and external intelligence agencies, AISI and AISE. They wanted the world to believe they were too ethical to work with a government that wouldn't play by the rules.
The Silence of the 'Ethical' Hacker
Fast forward to the present day, April 2026, and that principled stance looks more like a stage prop. Italian prosecutors, seeking to understand how and why Graphite was used against civilians, sent formal requests for information to Paragon via the Israeli government. A year later, the silence is deafening. No data, no logs, no cooperation.
This lack of transparency is a systemic issue in the private intelligence sector. From a compliance standpoint, these companies often hide behind the 'sovereignty' of their host nations. In this case, the Israeli government—which must approve the export licenses for these tools—appears to be the bottleneck. We have seen this script before. Spain’s High Court was forced to shelve its investigation into the targeting of Spanish politicians with NSO’s Pegasus spyware because Israeli authorities simply refused to cooperate.
In the legal world, we often talk about 'extraterritoriality'—the idea that a country can exercise authority beyond its borders. But when it comes to the spyware industry, the borders are built of thick, opaque glass. You can see the damage on the other side, but you can’t reach the person holding the hammer.
The American Paradox
What makes the Paragon case particularly nuanced is the company’s deep ties to the United States. While NSO Group was blacklisted by the U.S. Department of Commerce, Paragon has managed to keep its shoes clean in Washington. In fact, the company maintains an active contract with U.S. Immigration and Customs Enforcement (ICE).
ICE has told lawmakers that its law-enforcement arm, Homeland Security Investigations (HSI), uses Graphite to track drug traffickers and terrorists. This creates a jarring contrast: the same tool used to deport thousands of people in the U.S. is being investigated for targeting human rights activists and journalists in Europe.
This is the paradox of the dual-use technology market. A tool sold as a weapon against 'the bad guys' is almost inevitably used to silence 'the inconvenient guys.' When a company claims to have an 'ethical board' or 'stringent vetting,' we should be skeptical. Without binding, transparent, and enforceable international standards, 'ethics' is just a marketing department’s way of saying 'trust us.'
Privacy as a Fundamental Right, Not a Feature
Italy’s Prime Minister, Giorgia Meloni, has consistently denied that her government was behind the hacking of the Fanpage journalists. Yet, a forensic investigation by the prosecutors recently confirmed that Cancellato’s phone was indeed compromised. If the government didn't do it, and the company that made the tool won't say who did, we are left in a dangerous vacuum of accountability.
For the victims, this isn't an abstract debate about cyber-policy. For the activists at Mediterranea Saving Humans, this is about the safety of their operations and the lives of the people they are trying to save. When spyware is used against NGOs, it turns their digital footprints into a trail of breadcrumbs for those who would do them harm.
Ultimately, the Paragon saga proves that we cannot rely on the 'good intentions' of surveillance tech makers. Compliance should not be a choice; it should be a prerequisite for existence in the marketplace. When a company ignores a judicial request from a democratic ally, it shouldn't be allowed to keep its seat at the table of international commerce.
Protecting Your Digital Perimeter
While we wait for the regulatory landscape to catch up with the reality of digital espionage, there are actionable steps individuals—especially those in high-risk professions—can take to minimize their vulnerability. Think of your digital hygiene not as a chore, but as a suit of armor.
- Lock Down Your Cloud: Spyware like Graphite often targets cloud backups. If you don't need your messages backed up to the cloud, turn that feature off. Use end-to-end encrypted services that don't store metadata on their servers.
- Locking the Door with Hardware: For accounts that support it, use physical security keys (like Yubikeys) for two-factor authentication. This makes it significantly harder for an attacker to hijack your accounts even if they have your password.
- The Power of the Reboot: Many modern spyware strains are 'non-persistent,' meaning they live in the phone's temporary memory and are wiped when the device restarts. Developing a habit of daily reboots can be a simple but effective deterrent.
- Audit Your Permissions: Periodically review which apps have access to your microphone, camera, and location. If an app doesn't need a permission to function, revoke it. Digital minimization is your best defense.
We may never get a straight answer from Paragon, but we can make the 'Graphite' of the world much less effective by being proactive about our own digital rights.
Sources:
- General Data Protection Regulation (GDPR): Article 5 (Principles relating to processing of personal data) and Article 32 (Security of processing).
- European Court of Human Rights: Case of Szabó and Vissy v. Hungary (regarding the necessity of oversight in surveillance).
- Italian Code of Criminal Procedure: Articles regarding International Letters Rogatory and judicial cooperation.
- Wired Italy: Investigative reporting on the Paragon/Graphite Italian scandal.
- Citizen Lab: Technical analysis of Graphite spyware deployments.
Disclaimer: This article is for informational and journalistic purposes only and does not constitute formal legal advice. Privacy laws vary significantly by jurisdiction, and you should consult with a qualified legal professional regarding specific compliance or digital rights issues.



See you on the other side.
Our end-to-end encrypted email and cloud storage solution provides the most powerful means of secure data exchange, ensuring the safety and privacy of your data.
/ Create a free account

