Beeble Mail
Exchange end-to-end encrypted emails, on a daily basis.

Beeble Drive
Shield all your files with encrypted cloud storage.



Alexey Drobyshev

The Hades Campaign is a sophisticated worm targeting Python developers. It uses adversarial prompt injection to trick AI security tools and steals data.
Researchers demonstrate a self-replicating AI worm using local, open-weight models, bypassing traditional security to spread via semantic overflows.
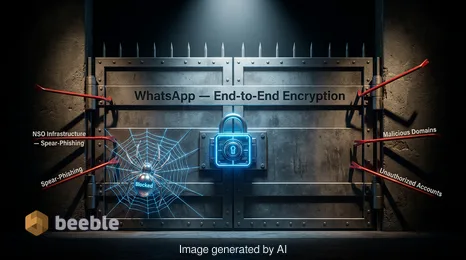
Meta blocks new NSO Group phishing attacks on WhatsApp and files a contempt order for violating a permanent injunction against the spyware vendor.

OpenAI introduces Lockdown Mode to protect ChatGPT users from prompt injection and data exfiltration. Learn how this setting secures sensitive data.

AI-powered autonomous worms are rewriting the rules of lateral movement. This briefing explores how CISOs must adapt to machine-speed exploitation.

Hackers tricked Meta's AI chatbot to hijack high-profile Instagram accounts. Learn how prompt engineering bypassed security and how to protect your data.

Analysis of the Dutch authorities' takedown of a 17-million device botnet and the systemic risks posed by residential proxy networks like Asocks.

Learn how to defend your Signal chat history from new phishing attacks targeting recovery keys and secure backups. Expert security analysis and tips.



Join us and become one of thousands utilizing our secured platform on daily basis.
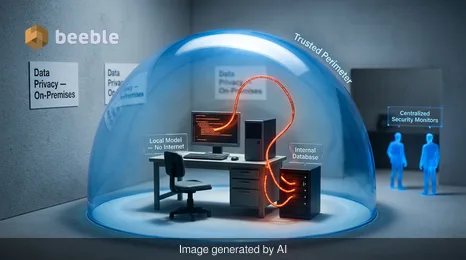
Our end-to-end encrypted email and cloud storage solution provides most powerful means of secure communication, ensuring the safety and privacy of your data.
/ Create free accountReg. No. 40203391789
VAT. No. LV40203391789
Skanstes Street 25
Riga, LV-1013, Latvia
Phone: +371 67821505
(not for support)
