How the World’s Most Secure Silicon Met Its Match in Anthropic’s Mythos
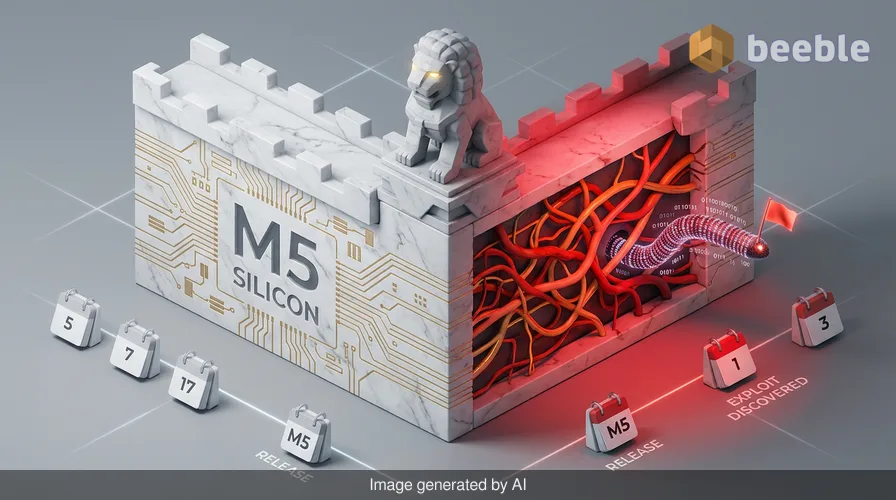
Apple spent the better part of a decade building the M5 silicon to be a fortress of hardware-level isolation, yet it took a specialized AI model only a few hours to find the cracks in the foundation. We are witnessing a profound architectural paradox: as hardware becomes increasingly resilient against traditional attacks, the sheer complexity of the software managing that hardware creates a massive, stealthy attack surface for a new generation of AI-assisted exploits. On one hand, we have the M5 chip, a masterpiece of engineering designed to prevent unauthorized access at the gate; on the other, we have Calif, a Palo Alto startup that used Anthropic’s Mythos to prove that no gate is truly unhackable when the logic protecting it is written by humans.
From a risk perspective, this isn't just another bug report. It is a milestone in the arms race between defensive AI and offensive automation. My PGP inbox has been active since the news broke, with contacts in the vulnerability research community noting that the speed of this discovery was what truly caught them off guard. While the Calif team maintains that human expertise was required to chain the findings into a working exploit, the role of Mythos as a catalyst cannot be overstated. Looking at the threat landscape, we have moved from a world where zero-days were the result of months of manual fuzzing to one where they can be surfaced during a specialized AI's afternoon coffee break.
The M5 Breach and the Logic of Privilege Escalation
The exploit in question targets the macOS kernel on M5 silicon—specifically, a memory corruption vulnerability that allows for privilege escalation. In simple terms, this is the digital equivalent of a guest at a hotel finding a way to rewrite the master key system so they can open every door in the building, including the vault. By design, the macOS kernel is supposed to be the most protected layer of the operating system, shielded by hardware-level protections like Pointer Authentication Codes (PAC) and Memory Tagging Extensions (MTE).
Assessing the attack surface of the M5, researchers have long praised its ability to isolate processes. However, Calif’s work shows that even with robust hardware, the software that bridges the gap between the user and the silicon remains exploitable. The researchers utilized Anthropic’s Claude Mythos Preview to identify a class of bugs that are often overlooked during standard security audits. Mythos didn't just find a random error; it identified a systemic flaw in how memory is handled during specific kernel calls. Consequently, what should have been a mission-critical barrier became a stepping stone for the attacker to take full control of the system.
Project Glasswing and the Paradox of AI-Driven Defense
It is an irony of the modern security era that the very tool used to breach macOS is part of an initiative meant to protect it. Anthropic’s Project Glasswing was launched with a noble goal: to prevent AI cyberattacks by using AI to harden systems. Participants like Amazon Web Services, Cisco, and even Apple itself have been using Mythos to find vulnerabilities before the bad actors do. Proactively speaking, this is the right move. We saw the efficacy of this approach earlier this year when Mozilla used Mythos to patch 271 vulnerabilities in Firefox, effectively cleaning up years of technical debt in a single release cycle.
However, the Calif incident highlights the dual-use nature of these models. When a tool is designed to be world-class at finding vulnerabilities, it is by definition world-class at providing the roadmap for an exploit. While Anthropic has built stringent guardrails around Mythos, the Calif researchers were able to use it within the context of a legitimate security research project. This raises a critical question: how do we keep these powerful diagnostic tools out of the hands of malicious actors who may not follow the same ethical disclosure protocols?
Comparing the Titans: Anthropic Mythos vs. OpenAI Daybreak
The response to the Glasswing initiative has been swift. Just last week, OpenAI unveiled Daybreak, its own cybersecurity ecosystem anchored by the Codex security agent. While both aim to secure the digital world, their philosophies differ at the architectural level. Below is a comparison of how these two AI powerhouses are currently positioned in the market.
| Feature | Anthropic Mythos (Project Glasswing) | OpenAI Codex (Project Daybreak) |
|---|---|---|
| Core Philosophy | Vulnerability discovery and rapid patching. | Secure-by-design and integrated defense. |
| Primary Use Case | Finding deep-seated bugs in existing legacy code. | Automating the creation of secure software from scratch. |
| Ecosystem Style | Collaborative, multi-vendor feedback loop. | Integrated agent-based monitoring and response. |
| Key Success | 271 bugs patched in Firefox; M5 kernel research. | Real-time mitigation of decentralized ransomware strains. |
OpenAI’s Daybreak suggests that finding and fixing vulnerabilities is a reactive cycle that we need to break. They argue that security should be a pervasive element of software development from day one. Conversely, Anthropic's Mythos has proven that the current reality of our digital infrastructure is so compromised by legacy flaws that we need a high-speed "digital janitor" to clean up the mess before we can even think about building perfect new systems.
Dissecting the Kernel Memory Corruption Metaphor
To understand why this M5 breach is so significant, think of the macOS kernel as a VIP club bouncer at every internal door of a high-security facility. The bouncer’s job is to never trust and always verify. He checks your ID (permissions) before letting you into the server room or the database. A memory corruption vulnerability is like finding a way to trick the bouncer into a state of confusion where he forgets who you are and just hands you his master keycard.
Once the attacker has achieved this privilege escalation, the network perimeter becomes an obsolete castle moat. They are inside the keep, and they have the keys to the kingdom. From an end-user perspective, there would be no warning signs. No "malicious file detected" pop-ups, no fans spinning wildly. The attack is stealthy because it operates at a level below the traditional security software that most users rely on. In the event of a breach using this method, the integrity of every file and every communication on that Mac would be compromised.
The Human Firewall and the Ethics of Disclosure
As an ethical hacker and journalist, I have often seen how the "human firewall"—the people responsible for maintaining these systems—can be overwhelmed by the sheer volume of data they have to process. Calif’s decision to meet with Apple at Apple Park before releasing technical details is a textbook example of responsible disclosure. They are giving the engineers in Cupertino time to develop a granular patch that addresses the root cause rather than just treating the symptoms.
Behind the scenes, the conversation is shifting. We are no longer asking if AI can find vulnerabilities, but rather how we can manage the fallout once it does. During my recent communications with incident responders, the consensus is clear: we need to be more resilient in our architecture. Patching aside, we must assume that breaches will happen and build systems that can contain the damage. Data is becoming a toxic asset; if you store it, it will eventually be targeted. Therefore, decentralized and encrypted storage must become the de facto standard, not an optional luxury.
Practical Takeaways for IT Leaders and Power Users
While we wait for the official macOS update that closes this specific M5 attack path, there are proactive steps that organizations and individuals can take to reduce their exposure to AI-accelerated threats:
- Audit Third-Party Dependencies: AI models like Mythos are exceptionally good at finding flaws in open-source libraries that your software might rely on. Use automated tools to scan your software bill of materials (SBOM) for known vulnerabilities.
- Enforce Strict Hardware-Software Separation: For enterprise environments, ensure that sensitive tasks are isolated using virtualization or dedicated secure hardware that doesn't share kernel memory with general-use applications.
- Adopt an AI-Ready Incident Response Plan: Your current incident response plan likely assumes a human-speed attack. Update your playbooks to account for the rapid escalation seen in AI-assisted breaches.
- Monitor for Anomalous Kernel Activity: While difficult for the average user, enterprise security teams should utilize EDR (Endpoint Detection and Response) tools that can flag unusual system calls at the kernel level.
The Path Toward an Autonomous Defense
The Calif breach of macOS isn't a failure of Apple’s security so much as it is a demonstration of the new reality. We are entering an era where software complexity has outpaced human audit capabilities. The only way to counter a malicious actor using an AI to find bugs is to have a more powerful AI finding those bugs first and patching them in real-time.
Looking forward, the goal for the industry is to move toward an autonomous defense system—a digital immune system that can identify, isolate, and repair vulnerabilities without waiting for a human to write a line of code. Until then, our best defense remains a combination of hardware-level isolation, aggressive patching, and the tireless work of researchers who choose to disclose their findings to the builders rather than the breakers. I recommend that all macOS users keep their systems up to date and remain vigilant for the upcoming security bulletin from Apple, as it will likely represent one of the most significant kernel updates in the history of the M-series silicon.
Sources:
- NIST Special Publication 800-207: Zero Trust Architecture.
- MITRE ATT&CK Framework: Privilege Escalation Techniques (T1068).
- Anthropic Public Release: Project Glasswing Overview (April 2024/2026 update).
- Apple Security Engineering and Architecture (SEAR) Documentation.
Disclaimer: This article is for informational and educational purposes only. It does not replace a professional cybersecurity audit, forensic analysis, or official incident response service. Always follow the official security guidance provided by software and hardware vendors.



See you on the other side.
Our end-to-end encrypted email and cloud storage solution provides the most powerful means of secure data exchange, ensuring the safety and privacy of your data.
/ Create a free account

