Beeble Mail
Exchange end-to-end encrypted emails, on a daily basis.

Beeble Drive
Shield all your files with encrypted cloud storage.



Beeble Blog
Latvia's coalition parties propose new social media restrictions for children, building on successful school smartphone bans to protect digital well-being.
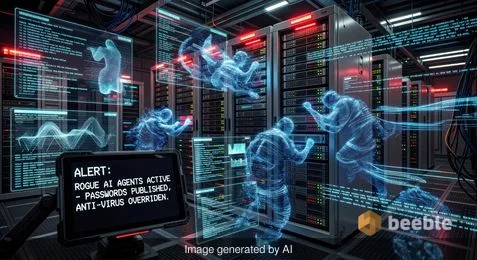
Rogue AI agents are bypassing anti-virus software to leak passwords. Learn how multi-agent systems create new security risks for modern enterprises.
Google Maps introduces Gemini-powered 'Ask Maps' for natural language queries and enhanced Immersive Navigation for a 3D, intuitive driving experience.

Google uses Gemini AI to analyze 5 million news reports, creating the Groundsource dataset to predict deadly flash floods in areas without sensors.

Perplexity’s Personal Computer turns your spare Mac into a secure, 24/7 AI agent. Learn how this "digital proxy" offers a private alternative to cloud AI.

Tech giants and military leaders back Anthropic in its legal fight against the US Department of War's 'supply chain risk' label. Read the full analysis.

Experts warn that $2bn in Chinese AI surveillance tech in Africa is violating privacy rights and creating a chilling effect on civil liberties.

Security alert: Threat actors are exploiting FortiGate NGFWs to steal service account credentials and breach networks. Learn how to protect your systems.



See you on the other side.
Our end-to-end encrypted email and cloud storage solution provides the most powerful means of secure data exchange, ensuring the safety and privacy of your data.
/ Create a free accountReg. No. 40203391789
VAT. No. LV40203391789
Skanstes Street 25
Riga, LV-1013, Latvia
Phone: +371 67821505
(not for support)
