The Glass Shield: Why Apple’s ‘Hide My Email’ Can’t Block a Federal Warrant
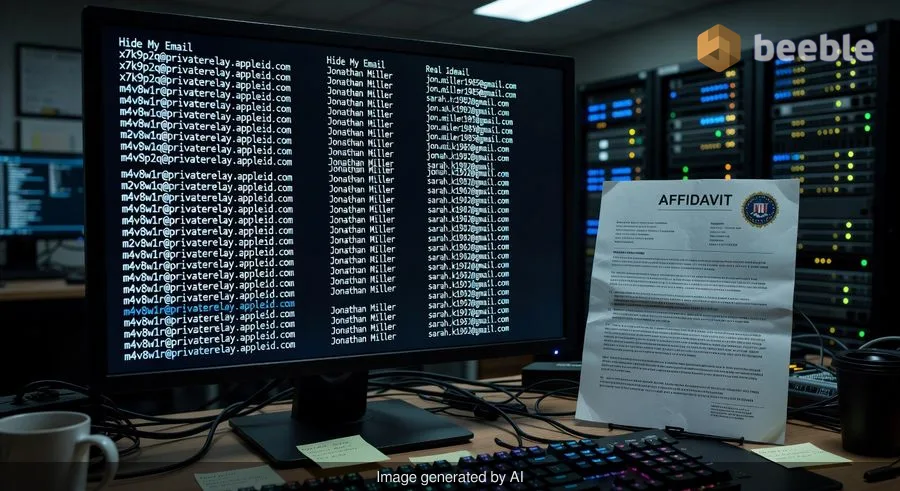
Earlier this month, a court affidavit revealed a striking reality for millions of iCloud+ users: Apple provided federal agents with the real identities of customers who thought they were operating behind a digital mask. As part of an investigation into threats made against Alexis Wilkins, the girlfriend of former government official Kash Patel, the FBI successfully requested records from Apple that unmasked a ‘Hide My Email’ address.
In response to the legal request, Apple didn’t just provide one name; they handed over the account holder’s full identity and records for 134 other anonymized email accounts created by the same user. This incident serves as a sophisticated reminder that in the world of big tech, privacy is often a granular service provided against commercial entities, not a systemic barrier against the state.
The Architecture of a Pseudonymous Identity
To understand how this happened, we must first look at the foundation of the house Apple built. ‘Hide My Email’ is a privacy-preserving feature that allows users to generate unique, random email addresses. These addresses act as a relay station: a newsletter or a retail site sends an email to the random address, and Apple forwards it to your personal inbox.
Apple is transparent about the fact that they do not read the content of these messages. However, the service is fundamentally pseudonymous, not anonymous. In a technical context, pseudonymity means that while your real name isn't visible on the surface, a master key exists that links the alias to the actual identity. Apple maintains the directory that connects ‘random-string-7@icloud.com’ to ‘john.doe@email.com.’ When law enforcement presents a valid statutory request, Apple simply consults that directory.
Privacy from Marketers vs. Privacy from the Law
Curiously, many users conflate digital hygiene with legal immunity. We use these features to avoid the intrusive gaze of data brokers and the persistent pestering of marketing algorithms. In this regard, the feature is robust. It prevents a shoe brand from selling your primary email address to a thousand other vendors.
Ultimately, however, Apple is a centralized data controller. Because they manage the infrastructure of the relay, they possess the metadata of the account’s existence. In a regulatory context, this is a precarious position for users who believe they are truly invisible. While Apple champions privacy as a fundamental human right, they also operate within a legal framework that requires compliance with court-ordered search warrants. To put it another way, the shield Apple gives you is made of glass—it’s great for seeing through and keeping the wind out, but it shatters when hit with the weight of a federal investigation.
The Digital Detective’s Perspective
As someone who meticulously audits privacy policies, I’ve often noticed the inconsistencies between marketing slogans and the fine print. When I receive a new device or service, the first thing I look for is the ‘Law Enforcement Support’ section of the transparency report. Most IT corporations claim they ‘care about your security,’ but as a researcher, I don’t believe it until I see how they handle a subpoena.
In my work, I apply the principle of data minimization not just to the articles I write, but to my own digital footprint. I often ask: ‘Is this information an asset or a liability?’ For Apple, the link between your alias and your real identity is a liability. It is a piece of data they are forced to store to make the service work, which inevitably becomes a target for investigators. This is the ‘patchwork quilt’ of modern privacy: a series of small protections stitched together that still leave significant gaps.
The Reality of the Handover
According to the court records first reported by 404 Media, the FBI’s request was part of a nuanced investigation into alleged threats. The affidavit states that Apple provided records indicating the anonymized account was associated with the ‘Target Apple Account.’
This highlights a systemic truth: if you are logged into an ecosystem—whether it’s Apple, Google, or Microsoft—your ‘anonymous’ features are tied to a billing method, a phone number, and a physical device ID. Notwithstanding Apple’s marketing, they are the ones holding the key to the labyrinth. If the police knock on their door with the right paperwork, Apple will unlock it.
Practical Steps for the Privacy-Conscious
If you use ‘Hide My Email’ or similar services, it is essential to understand their limits. These tools are excellent for managing your digital footprint and reducing the risk of an ‘oil spill’ (a data breach) at a third-party site from exposing your primary credentials. However, they are not a tool for whistleblowing or high-stakes anonymity.
| Feature | Protects Against | Does NOT Protect Against |
|---|---|---|
| Hide My Email | Data Brokers & Spammers | Federal Search Warrants |
| Email Forwarding | Primary Email Exposure | Service Provider Metadata Access |
| iCloud+ Encryption | Content Interception | Account Identity Discovery |
What to Do Next
To better protect your digital boundaries, I recommend taking these actionable steps:
- Audit Your Aliases: Go to your iCloud settings and review how many ‘Hide My Email’ addresses you have active. Delete any that are no longer in use to minimize your metadata footprint.
- Use Decentralized Alternatives: If your threat model requires true anonymity (e.g., for sensitive journalistic sources), consider using decentralized or end-to-end encrypted email services that do not require a link to a primary identity or phone number.
- Read the Transparency Reports: Periodically check Apple’s Transparency Report to see how many law enforcement requests they receive and how often they comply. This provides a clear-eyed view of the regulatory landscape.
- Practice Data Minimization: Don’t provide your real name or primary phone number to Apple if you intend to use their services for sensitive communication, though this is increasingly difficult within their ‘walled garden.’
Ultimately, privacy by design should be the foundation of our digital lives, but we must remain skeptical of any corporate promise that claims to be ‘impenetrable.’ True digital hygiene requires knowing exactly where the protection ends and where the law begins.
Sources:
- Federal Bureau of Investigation (FBI) Search Warrant Affidavit (re: Alexis Wilkins investigation).
- Apple Legal Process Guidelines for Government & Law Enforcement.
- Electronic Communications Privacy Act (ECPA).
- 404 Media / Court Watch reporting on FBI vs. Apple iCloud records.
Disclaimer: This article is for informational and journalistic purposes only and does not constitute formal legal advice. If you are facing a legal matter regarding digital privacy, please consult with a qualified attorney.



See you on the other side.
Our end-to-end encrypted email and cloud storage solution provides the most powerful means of secure data exchange, ensuring the safety and privacy of your data.
/ Create a free account

