

Cyber Security

Hackers are exploiting unpatched Windows Defender flaws leaked by a researcher. Learn about BlueHammer, UnDefend, and how to protect your organization.
Anthropic's Mythos model marks a shift to AI-driven exploit scaling. Learn how CISOs must adapt security architecture to survive the end of human-led hacking.

OpenAI revokes macOS certificates after a North Korean supply chain attack via Axios. Learn how the WAVESHAPER malware targeted the ChatGPT desktop app.

South Korea's PIPC fined Christie's KRW 287.2M for a phishing breach exposing 620 users' data due to weak passwords, no encryption, and delayed notice. Key fixes inside.
AI browser extensions are a massive, unmonitored security blind spot. Learn why these tools bypass DLP and how to secure your enterprise browser environment.

Uncover hidden dangers of shadow AI in enterprises: unapproved tools expose data and widen attack surfaces. Learn risks, real cases, and practical governance steps for secure adoption.
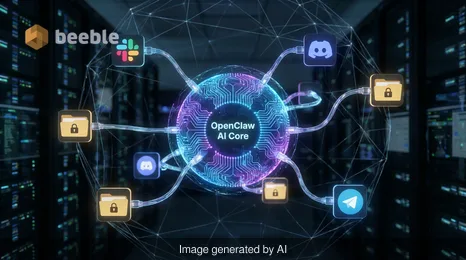
OpenClaw's CVE-2026-33579 vulnerability highlights the risks of agentic AI. Learn how a simple pairing request led to full administrative takeover.
GPUBreach attack exploits GDDR6 memory to gain root access. Learn how researchers bypassed IOMMU and what it means for AI and cloud security.



See you on the other side.
Our end-to-end encrypted email and cloud storage solution provides the most powerful means of secure data exchange, ensuring the safety and privacy of your data.
/ Create a free account

