Shielding Your Seed Phrase from the App Store’s Growing Shadow
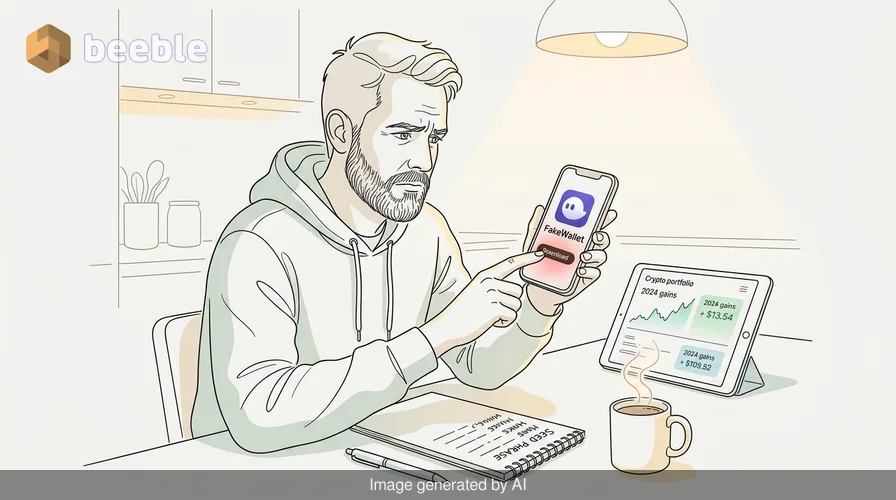
Imagine the scenario: You have been holding a modest amount of Ethereum and a few niche altcoins since the 2021 bull run. You are careful. You do not click on random Telegram links, and you never share your private keys. One Tuesday morning, you notice your favorite mobile wallet needs an update, or perhaps you decide to switch to a more reputable-looking interface you saw mentioned in a forum. You head to the Apple App Store—the proverbial gold standard of curated security—and download an app that looks indistinguishable from the official version of a major provider like MetaMask or Trust Wallet.
It opens with a slick, professional UI. It asks you to 'import your existing wallet' to get started. Naturally, you reach for your recovery sheet and type in those twelve words. Within seconds, the app displays a loading spinner. Behind the scenes, your seed phrase has already been exfiltrated to a command-and-control server in a jurisdiction where local law enforcement effectively looks the other way. By the time the spinner stops and the app throws a generic 'Network Error,' your digital vault has been emptied.
This is not a theoretical exercise in paranoia. In April 2026, security researchers have identified a cluster of 26 separate 'FakeWallet' applications that successfully bypassed Apple’s App Store Review Guidelines. These apps, collectively responsible for millions in lost assets, represent a sophisticated evolution in the threat landscape that targets the one thing encryption cannot protect: the human element.
The Illusion of the Walled Garden
For years, the Apple ecosystem has been marketed as a walled garden, a secure sanctuary where every piece of software is vetted by expert gatekeepers. From a risk perspective, this creates a dangerous psychological byproduct—the 'curation bias.' Users assume that if an app exists on the official store, it has been forensically scrubbed for malice. However, the reality of the App Store review process is often more about checking for API violations and UI consistency than deep-packet inspection or code-path analysis for obfuscated theft logic.
Assessing the attack surface of these 26 apps reveals a common, stealthy methodology. These were not 'day one' malicious apps. Often, they are submitted as benign utility programs—simple calculators, weather trackers, or basic fitness logs. Once they pass the initial review and gain a foothold on the store, the developers push a server-side update or use dynamic code loading to transform the interface into a crypto wallet clone. This bait-and-switch allows the malicious payload to bypass the initial bouncer at the door, only revealing its true nature once it is safely inside the VIP club of the user's device.
Dissecting the Anatomy of the FakeWallet
When we look at the threat landscape of 2026, we see that attackers have moved away from crude, buggy clones. The FakeWallet apps found this month were masterpieces of social engineering. They utilized high-resolution assets stolen directly from legitimate projects, perfectly mimicking the font, color schemes, and even the haptic feedback of the real applications.
By design, these apps do not attempt to hack the device’s operating system. They do not need to exploit a zero-day in iOS. Instead, they exploit the most pervasive vulnerability in the decentralized finance world: the requirement that a user must, at some point, provide their seed phrase to regain access to their funds. In terms of data integrity, the app itself remains 'functional' in the eyes of the OS; it is simply a form that sends data to a remote destination. To the operating system, this looks like any other authorized data transmission. To the user, it is a digital Trojan horse that hands over the keys to the castle.
I recently spoke with a source in the incident response community—communicating, as always, via an encrypted Signal thread—who had been tracking the movement of funds from one of these fake MetaMask clones. They noted that the attackers were using automated scripts to sweep funds the millisecond a seed phrase was entered. There was no manual intervention. It was a cold, mechanical execution of a theft that turned a user's mission-critical savings into a toxic asset in under thirty seconds.
The Structural Failure of Centralized Stores for Decentralized Assets
There is an inherent architectural paradox when we download tools for decentralized finance from a centralized marketplace. Looking at the situation through the lens of the CIA Triad—Confidentiality, Integrity, and Availability—we see a massive failure in confidentiality. The moment that seed phrase leaves the physical realm (the paper it was written on) and enters a digital interface that hasn't been verified through a cryptographic hash, the game is over.
Apple’s review process, while robust for general consumer apps, is not built to verify the destination of every string of text entered into a text box. Consequently, the responsibility for verification falls entirely on the end-user. In the security world, we often talk about the network perimeter as an obsolete castle moat, and this is a prime example. The perimeter is no longer the App Store’s boundary; the perimeter is the screen of your iPhone.
Behind the scenes, the developers of these 26 apps used sophisticated obfuscation techniques to hide the destination URLs of the stolen data. They didn't send the seed phrases to a blatant 'theft.com' domain. Instead, they utilized compromised legitimate infrastructure or obscure cloud functions that looked like standard analytics traffic. This makes forensic analysis after the fact difficult, as the traffic blends in with the background noise of a modern smartphone.
Proactive Defense in an Era of Stealthy Clones
So, how do we build a more resilient posture against this type of pervasive threat? Patching aside, because there is no 'patch' for a user voluntarily typing in their secret key, we must turn to more stringent operational security.
First, we must treat the act of entering a seed phrase into a mobile device as a high-risk event. In my own practice, I treat every new app as compromised until proven otherwise. This is the essence of the 'Zero Trust' philosophy: never trust, always verify. Before you download a wallet app, do not rely on the App Store’s 'Search' function alone. Go to the official website of the wallet provider (verified via multiple independent sources) and follow their direct link to the store. This ensures you are not falling for a typosquatted name or a paid ad that has gamed the search rankings.
Secondly, the use of hardware wallets—the shatterproof digital vaults of the crypto world—is no longer optional for anyone holding significant assets. By using a hardware wallet, your seed phrase never touches the internet-connected environment of your phone. Even if you accidentally download a FakeWallet app, the app can only request a signature for a transaction. It cannot see your seed phrase. You become the VIP club bouncer, and the fake app is stuck at the door without the right credentials.
The Human Firewall: Your Final Line of Defense
At the end of the day, these 26 apps were successful because they bypassed the human firewall. They relied on our fatigue, our trust in established brands, and our desire for convenience. As a countermeasure, we must cultivate a healthy paranoia. If a wallet app asks for your seed phrase unexpectedly—especially after an 'update'—your alarm bells should be deafening.
Legitimate wallet updates almost never require you to re-enter your seed phrase unless you have deleted the app and are reinstalling it. Even then, you should verify the app's authenticity by checking the 'Developer' field in the App Store. Look for a long history of updates and a high volume of legitimate, varied reviews. Beware of apps with thousands of five-star reviews that all sound suspiciously similar or were all posted within the same 48-hour window; these are often the result of review farms used to mask a malicious intent.
Key Takeaways for Digital Asset Protection
- Verify the Source: Never search for a wallet app directly in the App Store. Always navigate to the official project website (e.g., metamask.io) and use their 'Download' link to ensure you are directed to the legitimate listing.
- Hardware is King: Use a hardware wallet (like Ledger, Trezor, or BitBox) for any assets you do not plan to trade daily. These devices keep your seed phrase offline and immune to app-based phishing.
- Audit Your Apps: Periodically review the apps on your phone. If you have multiple wallets, consolidate them. A smaller attack surface is a safer attack surface.
- Beware the 'Migration' Lure: The most common social engineering tactic used by these 26 apps was the claim that a 'network upgrade' or 'wallet migration' required the user to re-input their seed phrase. This is a red flag 100% of the time.
- Monitor Your Accounts: In the event of a breach, time is of the essence. Use tools that alert you to outgoing transactions from your addresses so you can attempt to move remaining funds if the theft is not an immediate 'sweep.'
Sources
- NIST Special Publication 800-63 (Digital Identity Guidelines)
- MITRE ATT&CK Framework: T1477 (App Request Phishing)
- ENISA Threat Landscape Report 2025/2026
- Apple App Store Review Guidelines (Section 5.1: Privacy and Data Collection)
Disclaimer: This article is provided for informational and educational purposes only. Cybersecurity is a rapidly evolving field, and the techniques described herein may change. This content does not replace the need for a professional cybersecurity audit or dedicated incident response services. Always perform your own due diligence when managing digital assets.



See you on the other side.
Our end-to-end encrypted email and cloud storage solution provides the most powerful means of secure data exchange, ensuring the safety and privacy of your data.
/ Create a free account

