Securing the Browser Blind Spot Before AI Extensions Drain Your Enterprise Data
We spend millions of dollars on the digital equivalent of a fortress. We have the perimeter firewalls, the endpoint detection and response (EDR) agents, and the zero-trust identity providers acting like a VIP club bouncer at every internal door. Yet, while we are busy hardening the front gate, our employees are essentially handing out master keys to the back door, one 'helpful' AI browser extension at a time.
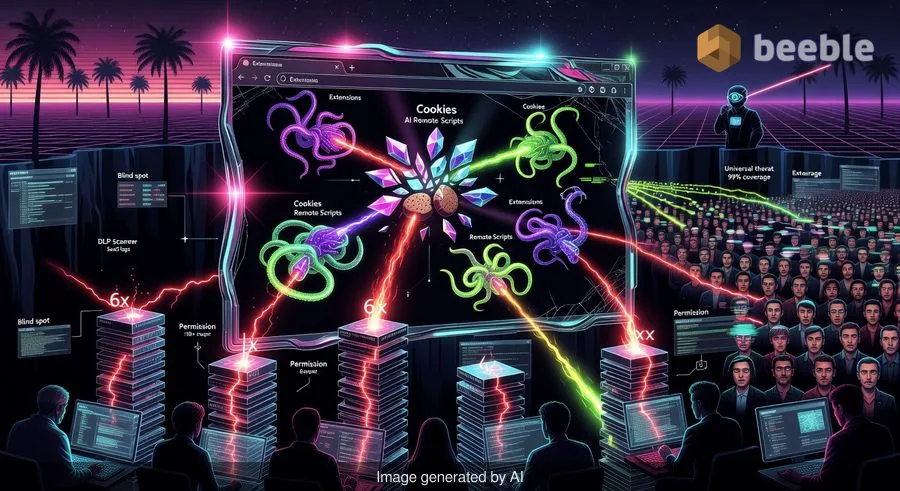
From an architectural level, there is a glaring paradox in modern enterprise security. We have built robust systems to monitor 'shadow' AI—those unauthorized ChatGPT accounts or unsanctioned LLM playgrounds—but we have almost zero visibility into the tools that live inside the browser itself. These extensions don't just visit the data; they live where the data is born.
The Dark Matter of the Corporate Network
In my years covering APTs and analyzing breach post-mortems, I’ve often seen security teams struggle with what I call the 'dark matter' of the network: things that are invisible but exert a massive, risky pull on the environment. Browser extensions are the ultimate dark matter.
According to a recent report from LayerX, this isn't a niche problem for the 'tech-savvy' crowd. A staggering 99% of enterprise users run at least one browser extension, and more than a quarter of your workforce likely has over 10 installed. We aren't talking about simple ad-blockers anymore. We are talking about AI-powered 'copilots' that summarize every email, 'productivity' tools that read every document, and translation services that see every password reset screen.
Behind the scenes, these tools are operating in a wild-west environment. While a SaaS application might require an OAuth handshake and a review of its privacy policy, a browser extension is often a one-click install that bypasses the standard procurement and security review process entirely.
Why AI Extensions Are Quantifiably More Dangerous
It is easy to dismiss extensions as a minor nuisance, but the data suggests a much more systemic risk. AI-focused extensions are not built like traditional software; they are often rushed to market to catch the generative AI gold rush. Consequently, they are 60% more likely to have a vulnerability than the average extension.
From a risk perspective, the permissions these tools demand are breathtaking. AI extensions are three times more likely to have access to browser cookies than their non-AI counterparts. In the hands of a malicious actor—or even a compromised developer—those cookies are the keys to the kingdom, allowing for session hijacking that bypasses even the most stringent multi-factor authentication.
Furthermore, these tools are 2.5 times more likely to be able to execute remote scripts. This means the extension you installed today as a grammar checker could, via a silent update tomorrow, become a delivery vehicle for malicious code. Assessing the attack surface here reveals a terrifying reality: these tools are six times more likely to have increased their permission requirements in the past year alone. This 'permission creep' is a stealthy way to move from 'reading site data' to 'controlling the browser.'
The DLP Vanishing Act
One of the most frustrating aspects of this threat for a SOC analyst is that traditional Data Loss Prevention (DLP) tools are often blind to it. Most DLP solutions look for data leaving the network or being uploaded to a cloud service. However, an AI extension lives inside the browser's execution context.
When an employee uses an extension to summarize a sensitive internal strategy document, that data isn't necessarily 'uploaded' in a way that triggers a network-level alert. The extension reads the DOM (Document Object Model) directly. It sees what the user sees. By design, it operates under the radar of traditional security stacks.
I once spoke with a white-hat hacker who demonstrated how a simple 'dark mode' extension could be modified to scrape credit card numbers from a checkout page. It didn't need to 'hack' the website; it just needed permission to 'read and change all your data on the websites you visit.' Users click 'Allow' without a second thought because they want the feature, not realizing they’ve just invited a digital Trojan horse into their session.
Moving Toward a Resilient Browser Strategy
Patching aside, the real solution isn't to ban extensions entirely—that's a losing battle against productivity. Instead, we need to treat the browser as a managed endpoint, not just a window to the internet.
Proactively speaking, organizations need to move away from reactive 'whack-a-mole' security and toward a granular governance model. This starts with visibility. You cannot secure what you cannot see.
Practical Takeaways for IT and Security Leaders:
- Conduct an Extension Audit: Use your endpoint management tools or specialized browser security platforms to generate a full inventory of every extension currently active in your environment. You will likely be surprised by the volume.
- Implement Risk-Based Scoring: Not all extensions are created equal. Prioritize the removal of extensions that demand 'high-risk' permissions, such as the ability to execute remote code or access cookies on all sites.
- Enforce Least Privilege at the Browser Level: Use Group Policy Objects (GPO) or browser management profiles to block all extensions by default, allowing only a curated 'allow-list' of vetted, mission-critical tools.
- Educate the 'Human Firewall': Employees often don't realize that an extension is a piece of software with full access to their digital life. Run a focused awareness campaign on the risks of 'one-click' AI tools.
In the event of a breach, the forensic trail often leads back to the path of least resistance. Right now, that path is paved with AI browser extensions. By the time an extension shows up in your SaaS logs as a malicious actor, the data is already gone. It’s time to close the window before the dark matter of the browser pulls your enterprise security into the void.
Sources:
- LayerX: 2024 Browser Security Report
- NIST SP 800-53: Security and Privacy Controls for Information Systems
- MITRE ATT&CK Framework: Browser Extensions (T1176)
Disclaimer: This article is for informational and educational purposes only and does not replace a professional cybersecurity audit or incident response service.



See you on the other side.
Our end-to-end encrypted email and cloud storage solution provides the most powerful means of secure data exchange, ensuring the safety and privacy of your data.
/ Create a free account

