The OpenClaw Incident: Why Your AI Agent Might Be a Stealthy Security Liability
When was the last time you handed the keys to your entire digital life to a software agent without a second thought? For hundreds of thousands of developers and power users, that moment arrived last November with the release of OpenClaw. It promised a frictionless future where an AI could shop for you, organize your files, and manage your Slack channels. But as we’ve learned this week, that convenience came with a precarious price tag.
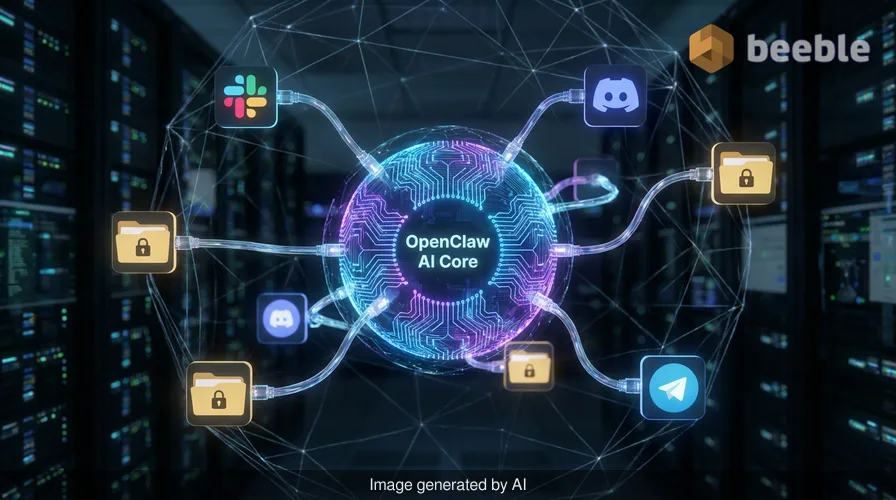
For more than a month, the security community has been sounding the alarm. OpenClaw, which has amassed a staggering 347,000 stars on GitHub, is designed to act as a digital surrogate. To be effective, it requires deep, pervasive access to logged-in sessions, local network files, and sensitive communication platforms. By design, it is built to bypass the traditional friction of manual task management. However, a recently patched vulnerability, CVE-2026-33579, has turned that surrogate into a potential digital Trojan horse.
The Architecture of a Takeover
At the architectural level, OpenClaw relies on a pairing system to authorize new devices. The flaw discovered by researchers at Blink was deceptively simple yet devastatingly effective. It allowed a user with the most basic permissions—known as operator.pairing scope—to silently elevate their status.
In practice, an attacker could send a pairing request that looked benign but requested operator.admin status. Because of a systemic failure in how the application validated these requests, the elevation happened without any secondary verification. Curiously, no user interaction was required beyond the initial handshake. From an end-user perspective, everything looked normal while the attacker was essentially handed the master keys to the kingdom.
I’ve spent years analyzing complex APT attacks, and this particular exploit reminds me of the classic 'broken elevator' logic: you press the button for the lobby, but the system lets you bypass the security badge reader to reach the penthouse. In the world of AI agents, the penthouse contains your mission-critical data, your private messages, and your stored credentials.
Assessing the Attack Surface
From a risk perspective, the impact of this vulnerability cannot be overstated. When we talk about privilege escalation, we often think of it as a single step in a long chain. Here, the escalation is the chain. Once an attacker gains administrative access to an OpenClaw instance, they aren't just inside a sandbox; they are operating with the full permissions of the host user.
For a corporate environment, this is the digital equivalent of an oil spill. The damage isn't contained to the initial point of impact. An administrative attacker can read connected data sources, exfiltrate credentials stored in the agent’s skill environment, and pivot to other connected services like Jira or AWS. Because OpenClaw is designed to be a robust assistant, it often has the 'keys' to various APIs already stored in its memory.
Ultimately, this vulnerability allowed for a full instance takeover. Thousands of instances may have been compromised over the last month, and because the exploit was so stealthy, many users may still be unaware that their digital surrogate has been moonlighting for someone else.
The VIP Club Bouncer: Why Zero Trust Matters
This incident serves as a perfect object lesson in why we need to treat AI agents with a healthy dose of paranoia. We often view these tools as helpful companions, but in a security context, they represent a massive expansion of the attack surface. We should think of zero trust as a VIP club bouncer at every internal door of our operating system. Just because you let the AI into the club doesn't mean it should have access to the back office without a constant, granular re-verification of its credentials.
OpenClaw’s developers have released a patch, but patching aside, the fundamental issue remains: we are granting autonomous agents more power than our current security frameworks are prepared to monitor. In a regulatory context, this raises significant questions about data integrity and unauthorized access. If an AI agent performs a malicious action on your behalf because it was compromised, who is liable?
Moving Toward a Resilient AI Strategy
If you are one of the 347,000 users who integrated OpenClaw into your workflow, your first step is obvious: update to the latest version immediately. However, simply plugging holes in a ship's hull isn't enough if the ship is fundamentally designed to take on water. We need to rethink how we isolate these agents.
Proactively speaking, organizations should implement the following steps to mitigate the risks of agentic AI:
- Audit Permissions: Use the principle of least privilege. Does your AI agent really need access to your primary email and your terminal? If not, revoke it.
- Isolate Environments: Run AI agents in containers or virtual machines that do not have direct access to your primary file system or sensitive network shares.
- Monitor API Calls: Keep a forensic log of the actions your AI agents take. If an agent starts making unusual tool calls or accessing files it hasn't touched in months, that’s a red flag.
- Rotate Credentials: If you suspect an instance was compromised, assume all stored API keys and session tokens are tainted. Rotate them immediately.
As we navigate this new landscape, we must remember that privacy and security are not just compliance checkboxes—they are the foundation of trust in the AI era. We cannot afford to let our desire for automation outpace our commitment to a robust defense.
Sources:
- Blink Security Research: Analysis of OpenClaw Privilege Escalation.
- National Vulnerability Database: CVE-2026-33579 Detail.
- OpenClaw GitHub Repository: Security Advisory and Patch Notes.



See you on the other side.
Our end-to-end encrypted email and cloud storage solution provides the most powerful means of secure data exchange, ensuring the safety and privacy of your data.
/ Create a free account

